[-] Vulnerable Software:
APfell/Mythic
[-] Software Description:
APfell/Mythic is a cross-platform, post-exploit, red teaming framework built with python3, docker, docker-compose, and a web browser UI. It’s designed to provide a collaborative and user-friendly interface for operators, managers, and reporting throughout mac and Linux-based red teaming.
[-] Product Description:
APfell/Mythic is a cross-platform, post-exploit, red teaming framework built with python3, docker, docker-compose, and a web browser UI. It’s designed to provide a collaborative and user-friendly interface for operators, managers, and reporting throughout mac and Linux-based red teaming.
[-] Software Website:
https://github.com/its-a-feature/Apfell
https://github.com/its-a-feature/Mythic
[-] Software documentation:
https://docs.apfell.net/
[-] Vulnerable Software version:
Ver ≤ 1.4
[-] TIme/Date of reporting:
Fri, Apr 17, 9:20 AM CT
[-] Vulnerability Type, Impact and more info:
Cross-Site Scripting
[-] Vulnerable Request Type:
Reflected, GET based
[-] Vulnerable Module/Parameter/Path:
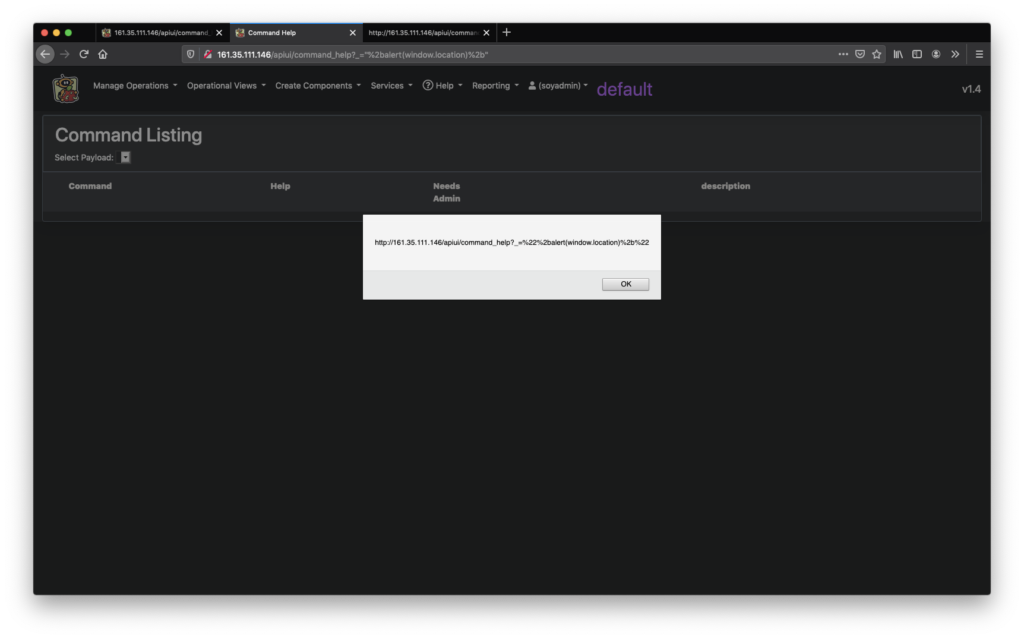
APfell_Installation_IP_OR_DOMAIN/apiui/command_help?_=%22%2balert(window.location)%2b%22
[-] Vulnerable Function:
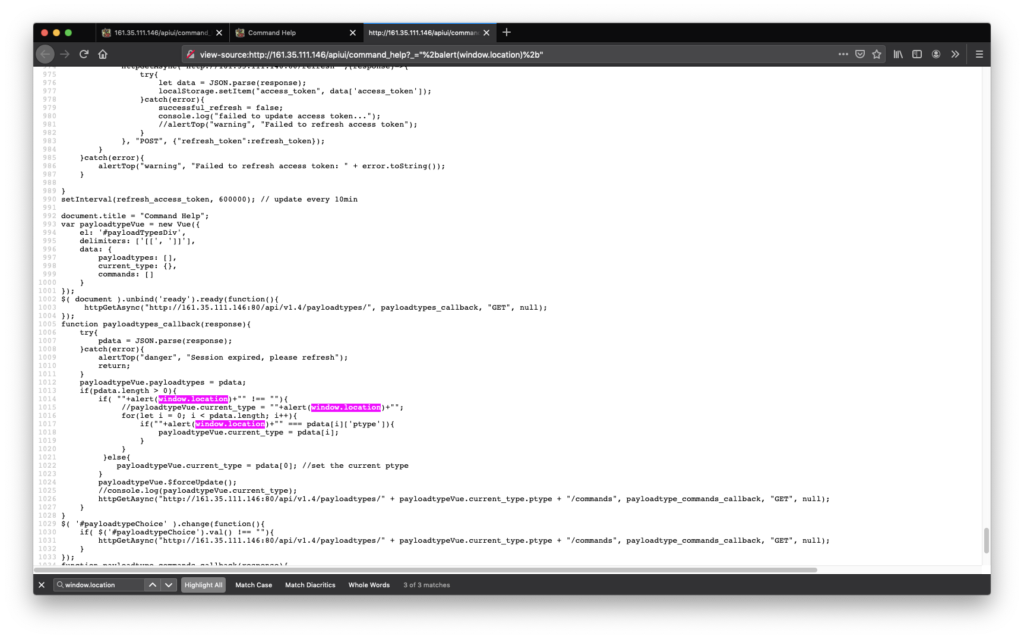
payloadtypes_callback
[-] Vulnerability overview
APfell/Mythic 1.4 is vulnerable to authenticated reflected Cross-Site Scripting (XSS) allows an attacker to steal remote admin/user session and/or adding new users to the administration pannel hence privileges escalation.
The vulnerable component was “/apiui/command_help” resulted in unfiltered user input to be passed to function “payloadtypes_callback” hence a javascript code will be executed in the context of the logged-in session.
function payloadtypes_callback(response){
..snip..
if( ""+alert(window.location)+"" !== ""){
//payloadtypeVue.current_type = ""+alert(window.location)+"";
for(let i = 0; i < pdata.length; i++){
if(""+alert(window.location)+"" === pdata[i]['ptype']){
payloadtypeVue.current_type = pdata[i];
}
}
}else{
payloadtypeVue.current_type = pdata[0]; //set the current ptype
}
..snip..
}
[-] Proof of Concept URL:
http(s)://APfell_Installation_IP_OR_DOMAIN/apiui/command_help?_=%22%2balert(window.location)%2b%22
[-] Fix Suggestion:
Properly sanitizing user inputs.
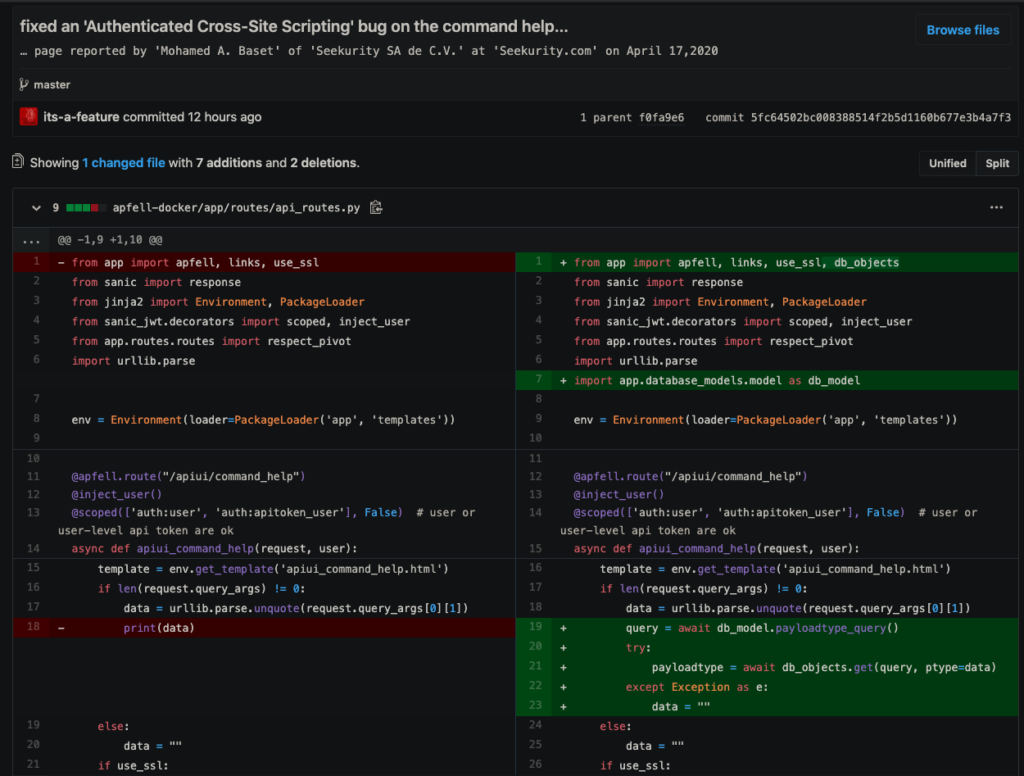
[-] Applied Fix:
https://github.com/its-a-feature/Apfell/commit/5fc64502bc008388514f2b5d1160b677e3b4a7f3
https://github.com/its-a-feature/Mythic/commit/5fc64502bc008388514f2b5d1160b677e3b4a7f3
[-] PoC:
[-] Product URL(s):
https://github.com/its-a-feature/Apfell
https://github.com/its-a-feature/Mythic
[-] Credit
Mohamed A. Baset (@SymbianSyMoh) Director of Cyber Security at @Seekurity SA de C.V.
[-] Advisory URL(s):
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-23014
https://github.com/its-a-feature/Mythic/commit/5fc64502bc008388514f2b5d1160b677e3b4a7f3
[-] Disclaimer:
This bug is subject to Seekurity SA de C.V. responsible disclosure rules which is a 90-day-disclosure-deadline. After 90 days elapse or a patch has been made broadly available, the bug details will become visible to the public through our official communication channels.
A minute if you please!
Building a website, an application or any kind of business? Already have one? Worried about your security? Think twice before going public and let us protect your business!

Previous Next