What is Cookie stuffing fraud?
Is an activity which allows actors online to defraud affiliate marketing programs by causing themselves to receive credit for purchases made by web users (for this case users who made an online purchase in Amazon, Walmart, eBay or any other Online Store), even if the affiliate marketer didn’t actively perform any marketing for the affiliate program. It occurs when a fraudulent publisher, tricks a web user’s browser into visiting an Online Store, that the web user didn’t intent to visit. This links causes to the Online Store to record that the publisher generated the “sale” and gives the fraudulent publisher credit for any purchases the web user might make.
How it works?
There are many ways to do this, when a fraudulent publisher control a website or have broken into a website they do not control.
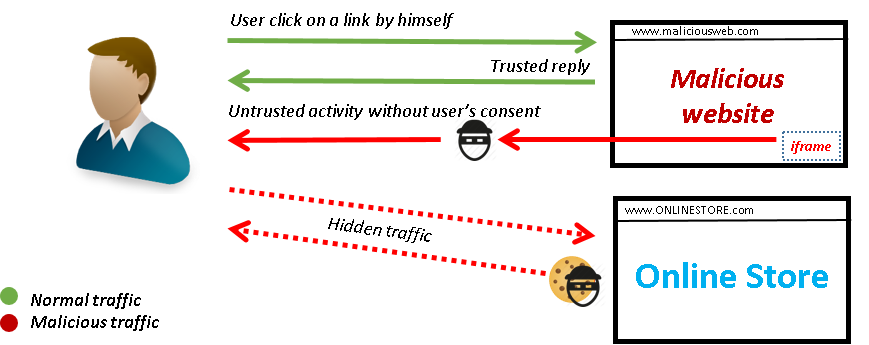
1. The fraudulent publisher could add a hidden iframe element (commonly in tiny images) in a site, and set this iframe to an affiliate link to any Online Store domain. The fraudulent party would set the affiliate link to include their affiliate identifier, causing to the Online Store process this request as though the fraudulent publisher encouraged the web user to visit the Online Store website. When the Online Store processes this request, they set a cookie on the web user’s browser, now giving the fraudulent Publisher credit for delivering the web user.
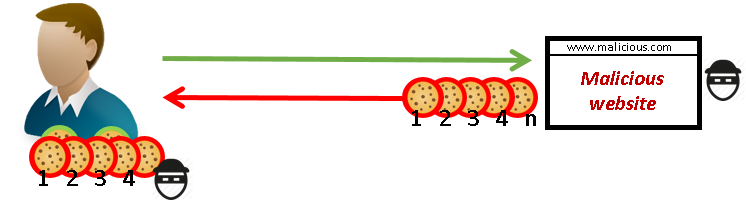
2. Another similar process could permit, overwrite any record that the web user was previously referred by an honest Publisher.
a) A customer visit a trusted affiliate website.
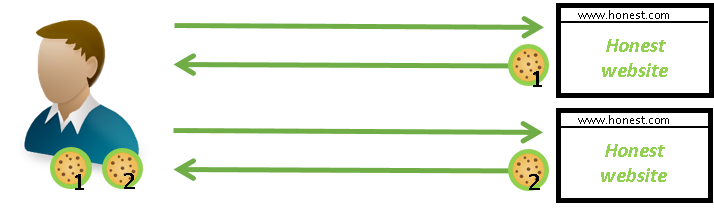 b) The customer arrives to a malicious website, this website injects malicious cookies and overwrites the honest.
b) The customer arrives to a malicious website, this website injects malicious cookies and overwrites the honest.
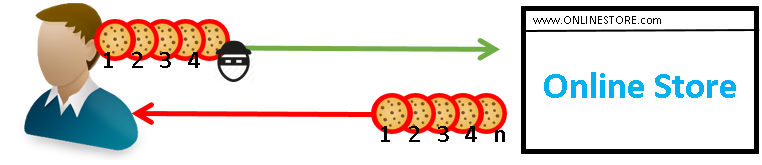
 c) Customer arrives to Online Store website, the site reads the malicious cookies, if the customer make a purchase, the payment will be to the malicious affiliate.
c) Customer arrives to Online Store website, the site reads the malicious cookies, if the customer make a purchase, the payment will be to the malicious affiliate.
3. Another way is based on malware installed on a web user’s machine that opens pages, pop ups or banners.
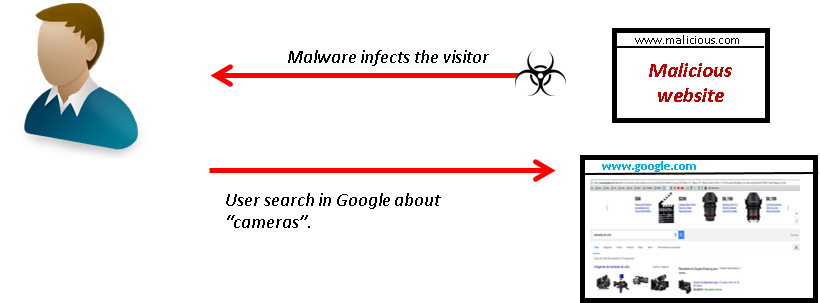 Malware starts showing advertise about the user’s search, if the user click on a link from google search to Online Store website, those malware generates and injects cookies with the malicious affiliate’s information.
Malware starts showing advertise about the user’s search, if the user click on a link from google search to Online Store website, those malware generates and injects cookies with the malicious affiliate’s information.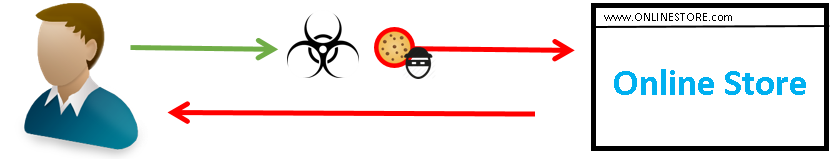
4. Another way is when a web user click on a malicious link or image, then he’s redirected to a website, but at the same time, he’s redirected to other websites without realising that. 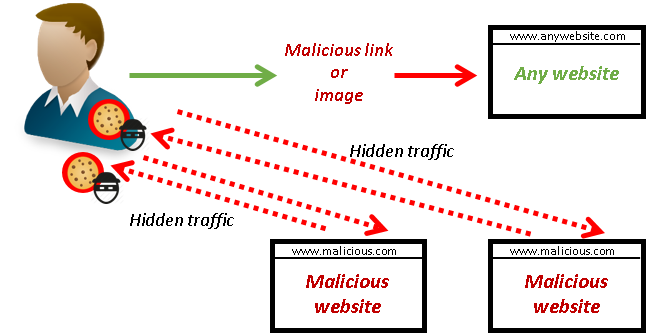
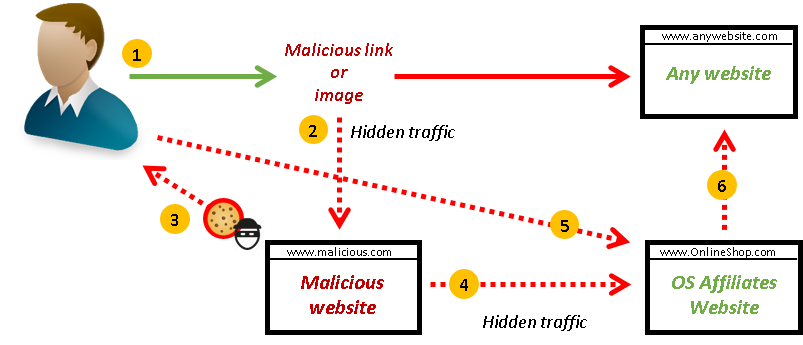
5. Another way is when a web user click on a malicious link or image, then he’s redirected to a website, but during the redirections in the background, he’s visiting a chain of websites.
Characteristics of a fraud
The principal characteristics to identify a fraudulent affiliate activity is as follows:
By suspicious request:
- To an affiliate’s site without user interaction.
- Redirections to the current window.
- Affiliate’s site is requested by an iframe.
- Flash elements made a cross domain request to an affiliate’s website.
- Requests made by any other way as images or scripts reference to affiliate’s website.
Referrer page:
- Not able to access the content of the referring page.
- Domain is expired.
Referrer time:
- Amount of time (seconds) that the web user spent on the referring page before clicking in a link.
Time spent on online retailer’s site:
- Amount of time the web user continued browsing the online retailer’s site after requesting the affiliate link. (2 seconds or less could be consider as a fraud).
Use of HTTPs
- HTTPs offered by referring site and redirections.
Cookie expiration time:
- Cookie never expire.
- Expiration time was set with more time that permitted by the Online Store.
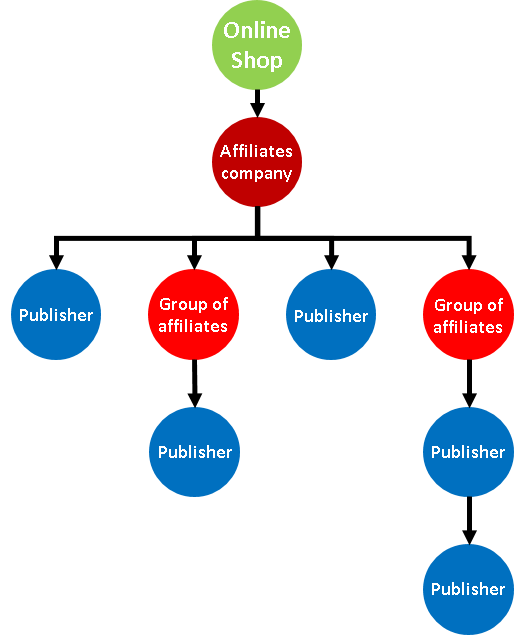
How Affiliates companies works
Affiliates companies work with 2 types of affiliates:
1.Direct affiliates (Publishers): who has blogs or sites whit it’s own users, visitors or traffic. They’re not depending of another source.
2.Group of affiliates: A group of publishers represented by an Affiliate company who works with the principal affiliate company as a Publisher.
It’s not east to track fraudulent activities with the second model. Trusted and untrusted redirections could be nested.
Normal traffic
To better understanding what is normal traffic, consider this example:
- OnlineStoreABC is running an affiliate marketing program.
- AffiliatesABC is a company for business analytics and marketing automation who has a group of publishers ready to introduce them to an affiliate marketing programs.
- PublisherABC is a website who shares offers, promotions and discounts. They are a part of the publishers group of AffiliatesABC.
AffiliatesABC provides to OnlineStoreABC, a publishers group to participate in OnlineStoreABC’s affiliate marketing program. One of them is PublisherABC, AffiliatesABC provides PublisherABC an affiliate identifier, such as “PublisherABC12345”, which he uses to identify his visitors in the program.
When a web user, goes to PublisherABC web site and he wants to purchase the product offered, he can click in the button “go to the offer” and PublisherABC web site injects in the user web browser a cookie with his identifier (PublisherABC12345), with this OnlineStoreABC knows that this customer was refered by PublisherABC12345.
Examples:
1. Result when a user types OnlineStoreABC’s URL in the address bar.
![]()
![]()
2. Result when a user is referred from Google search.
![]()
![]()
3. Result when a user is referred from a publisher website.
![]()
![]()
4. Result when a user is referred from a publisher under affiliate company.
![]()
![]()
About some publishers and affiliates groups
One of the most useful vulnerabilities to commit cookie stuffing, is through a XSS. Some publishers and affiliates groups have this type of vulnerabilities and an attacker with a basic knowledge about XSS can exploit it. It can be used to redirects traffic to an attacker servers or compromised sites, inject malicious cookies or erase trusted cookies.
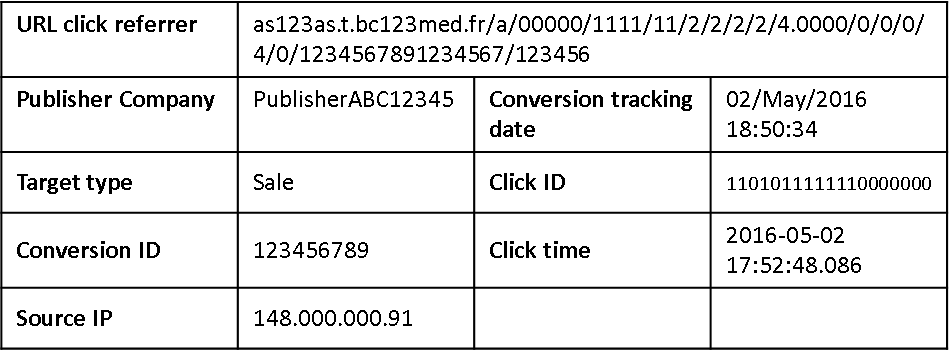
Fraud detections
We took a URL from our traffic logs. This URL referrer isn’t clear, we can’t identify the link owner, where it comes from and where it goes.
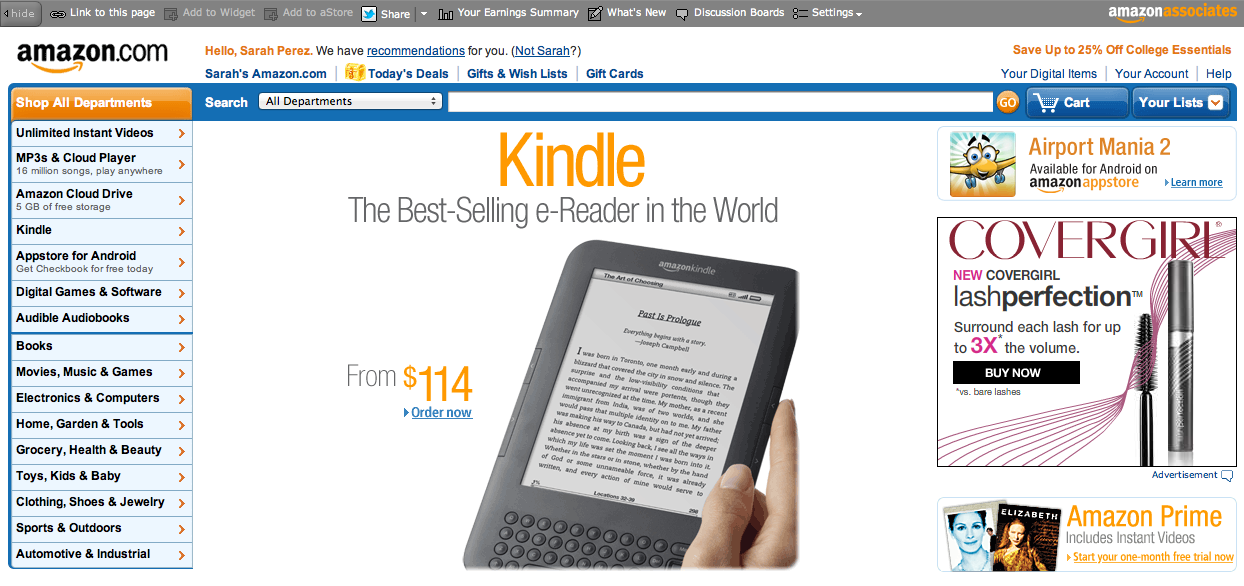
Browsing to the link, an image with the old Amazon website appear. (For this example we’re using an old image from Amazon website, this wasn’t the real one).
Clicking on the image, web user is redirected to a parked website, but this only works one time. The next try, the page gives a message: “expired”.
Doing a query to the URL, we can track the traffic, starting when the web user click on the imagen until he arrives to a parked site.
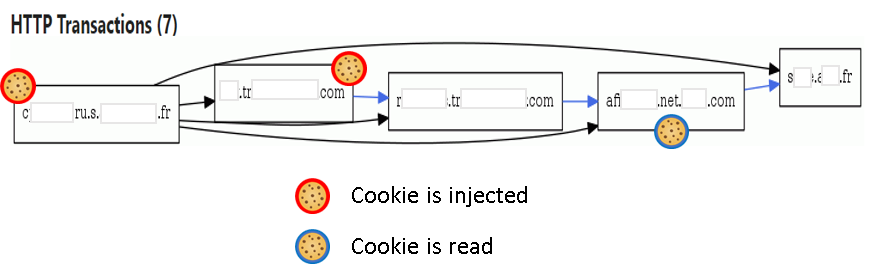
A chain of requests between servers from Sweden, France and Ireland are involve when a web user click in the image.
URLs identified
anyurlxxxxx.fr
This aparently is not a malicious domain, but some adware developers are using it to obtain revenues. The adware shows offers, coupons, pop ups with similar images as the original websites, sometimes this images are outdated. During our investigation, we notice a request to an image from x-mas season (For this example we will use an amazone’s image again). Web users can’t see this image but when the browser is loading the image at the same time is requesting an URL.

All this links aren’t available after the first click.
How websites are tracking us.
Cookies can store more data that we can imagine. Is not only about our preferences, cookies can store more than that and the most importar is about the average life time. During the redirections, sites injected 10 cookies, 4 of them are persistent with the average life time of 365 days.
| Type of cookie | Cookies |
| Session cookies are cleared when you close your browser and allow the website to identify user’s state — such as logged-in users. They are mostly considered harmless because they cannot be used for long-term user tracking. | 2 |
| Third-party domains is the count of organizations allowed by the webmaster to trace your across the site. These cookies may be set for various purposes, like tracking ads displayed on the website, collection of statistics, targeted advertising etc. | 4 |
| Persistent cookies are the cookies that are preserved through browser shutdowns. This means, even if you close this page today and ever return there in future, the website will know you’re a returning visitor. This may be used for “remember me” features, as well as persistent user tracking. These cookies, especially if set by third party organizations, are powerful tool for monitoring your activities across all the websites you visit. This cookies does not set httpOnly and can be read by JavaScript. This might be a problem if this cookie contains an authentication-related session token |
4 average life-time of 365 |
Next steps
- Safe the referrers information in your systems.
- Make a procedure to evaluate affiliates with online blacklists, considering why this affiliate is blacklisted.
- Revision of domains in Google, if they have been identified by someone as adware.
- Display affiliate disclosure on affiliate’s website: Inform to the customers that they are in an affiliate website and they may be paid a commission for promoting products on the website. Being open and honest about what type of website our customer is using, you are ensuring your customers are not being misled in any way by your marketing practices.
- Develop new policies about customer protection against unfair trading, prohibiting ‘misleading actions’.
- Full disclosure policy:
- The disclosure must be on every page of affiliates site that promotes Online shop products.
- The disclosure must be visible above the fold, clearly seen by the visitor without the need to scroll down the page.
- Affiliates evaluation policy against unfair activities
- Displaying trust marks, quality mark or equivalent without having obtained the necessary authorization.
- Claiming that an affiliate (including his business practices) has been approved, endorsed or authorized by Online Shop without complying with the terms of the approval, endorsement or authorization.
- Falsely stating that a product will only be available for a very limited time, or that it will only be available on particular terms for a very limited time, in order to elicit an immediate decision and deprive consumers of sufficient opportunity or time to make an informed choice.
- Use of adware or malware to obtain higher revenues or illegal activity related to malware traffic.
- Stablish a best practice framework to help the company;affiliate market in a honest, legal and ethical way.
- Set a cookie expiration date in company’;policies and agreements with affiliates.
- Review logs comparing the purchase date vs the click date, to verify that the purchase was made inside the approved period by the company.
- Add in all the agreements with the affiliates about the forbidden activities as use of iframes, Dynamic iFrames, use of adware tools.
- Ban companies who use toolbars, tool bars can be helpful to commit frauds called cookie stuffing 2.0.
- Establish a procedure to open an investigation to the affiliates who are obtaining most money per month.
- For fraudulent affiliates:
- Stop operations/deals with fraudulent affiliates identified.
References
-
- https://www.affiliatedisclosure.com/
-
- https://moreniche.com/news/affiliate/the-affiliate-disclosure-policy-whats-it-all-about/
-
- http://www.legislation.gov.uk/uksi/2008/1277/schedule/1/made
- http://www.affiliatefix.com/http://www.webmaster-money.org/category/blacklist
Thanks for reading!
.
.
Hey!
Building a website? Or already built a one? Think twice before going public and let us protect your business!

Previous Next